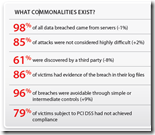
“79% of victims subject to PCI DSS had not achieved compliance” [close to what I suspect the reality is – a lot of organizations did try to ‘fake their way’ to PCI compliance. Hopefully now Bob’s point about ‘not compliant at the time of the the breach’ will make more sense – A.C.]
“Because fraud alerts are the leading method of discovering breaches, it stands to reason that many breaches could occur without anyone being the wiser if the criminal decided it was in his best interest to be patient“ and “We find it more than a little ironic that the most effective way of detecting data breaches is for the perpetrator to fraudulently use what was stolen.” [every time I read “fraud is the leading method of breach discovery”, I feel sad. To me this means either most organizations are negligent, or our security technology is crap. Or both :-)]
I am not touching the whole insider vs outsider debate again; it just smells. Read the report and forget the “80/20 myth.” Think about it though: every organization has 1-100,000 insiders (=employees, partners, contractors, etc), but there are possibly millions of criminal outsiders… Given how porous many networks are, who do you think will steal more?
“incredible 97% (!) of the 140+ million records were compromised through customized malware across the Verizon-USSS caseload.” [toss the AV, finally? – A.C.]
“The use of stolen credentials was the number one hacking type in both the Verizon and USSS datasets, which is pretty
amazing when you think about it.”
“We’ve observed companies that were hell-bent on getting patch x deployed by week’s end but hadn’t even glanced at their log files in months.” [given that password guessing – seen in logs – trumps vuln exploitation by such a wide margin, this should change. Will it? – A.C.]
“The security media hype machine would like us to believe that we’re all Targets of Choice [which is ‘cool’ and not Targets of Opportunity which is silly – A.C.] and there’s nothing we can do to stop the new [insert whatever you like here] threat. This simply isn’t true and is not a healthy line of reasoning for security management.” [indeed, ‘APT is for everyone’ message is pretty stupid. If your passwords on external routers are something like ‘password’, you have a long task list to go thru before ‘APT’ shows up – A.C.]
Breach discovery bar chart on the right is “The Saddest Picture Ever (TM)” :-) No comment really.
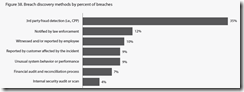
“It cannot be a pleasant experience to learn that the six months of log data you’ve been collecting contained all the necessary indicators of a breach. It is, however, a common experience. We consistently find that nearly 90% of the time logs are available but discovery via log analysis remains
under 5%.”
“In the 2009 DBIR, we reported that event monitoring and log analysis, which should be the doyen of detection, successfully alerted only 6% of breach victims. This year that figure has dropped—yes dropped—to 4%. Of that 4%, log analysis lead to the discovery of a handful of breaches while intrusion detection systems identified only one.” [‘Richard, IDS really is dead’ :-) or The Second Saddest Fact in the report - A.C.]
“Change your approach to event monitoring and log analysis: A quick review of a few findings from this report will set the stage
for this one. 1) In most attacks, the victim has several days or more before data are compromised. 2) Breaches take a long time to
discover and 3) when that finally happens, it usually isn’t the victim who finds it. 4) Finally, almost all victims have evidence of the
breach in their logs.” [this, BTW, reminds us that ‘detection within days’ is darn right close to ‘real-time’ for most organizations… – A.C.]
Get full report here.
Enjoy!
